This is the continuous integration build, it is not an authorized publication, and may be broken or incomplete at times. Refer to the Directory of published versions for stable versions
Security Workflow
The ePrescribing and ISB systems require conformant calling systems to assert that they have already authenticated the users in their system, and that they are passing the details of this individual to the ePrescribing Identity Server to exchange for an access token that they can connect to the FHIR Resource servers (either the ePrescribing or ISB API).
This sequence implements the OAuth 2 token exchange flow, and involves a Client Application, the Identity Server and the FHIR Resource Server.
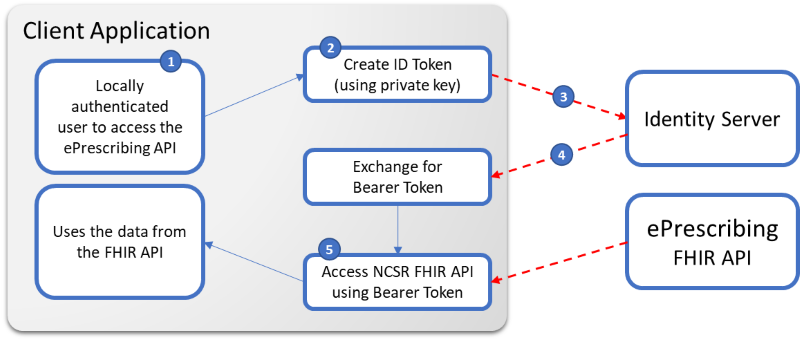
- The Client Application internally ensures that the user is authenticated with their system (not the ePrescribing system)
- The Client Application creates an Identity JWT and signs with their private key
- The Client Application calls the Identity Server to exchange it for an Access Token, posting:
- Signed JWT
- Client ID & Client Secret
- Requested Scopes
- The Public Key corresponding to their private key in a custom header (if using digital certificates - i.e. NASH Certs, which must be the certificate registered with eRx or Medisecure)
- The Identity Server returns an Access Token that can be used till it expires (which may only be 30 minutes), at which point the Client application will need to re-authenticate (as described in point 2)
- All access to the FHIR Resources servers requires the Access Token to be presented as a Bearer in the Authorization Header (except for the FHIR Capabiltiy Statement)
Note: Even in the case where the API token is not being used, the Client Certificate must be used to connect ensuring that only access to systems involved in healthcare access it.
A detailed walkthrough of this workflow can be found in the Authentication & Authorization guidance section.
All connections must be made via https using TLS 1.2
Audit and Privacy
The following security conformance requirements must be met by systems connecting to the ISB:
- As the Digital Certificate provides a B2B style authentication mechanism, The PMS system must ensure that only authorized users are able to access the ePrescribing/ISB system using this secure connection.
- Records downloaded from ePrescribing/ISB must be tagged to indicate that they came from ePrescribing/ISB, and must be secured accordingly.
- Medical information should always be treated securely, and not exposed to other non authorised people or systems.
External Security References
The following set of links provide additional guidance from the FHIR community on other best practices in FHIR implemenations, which were considered when developing the security guidance above, along with other existing authentication practices already in use by PMS systems.